Last mile security between AI agents and enterprise APIs
Automate API security across AI agent workflows
Last mile security between AI agents and enterprise APIs
Automate API security across AI agent workflows
Trusted
by security & development teams globally













Deterministic guardrails securing AI Agents
Automate agentic AI security controls from design to build to runtime
API Security Audit & Scan
Design & Dev Time Guardrails
- OpenAPI contract governance
- Audit to AI remediation loop
- Scan to AI Agent remediation loop
- Development Security Quality Gates
API Security Governance
Build Time validation Guardrails
- Scan for implementation vulnerabilities
- Runtime Security Quality Gates
API Protection
Runtime Protection Guardrails
- Secure MCP Server validate inputs
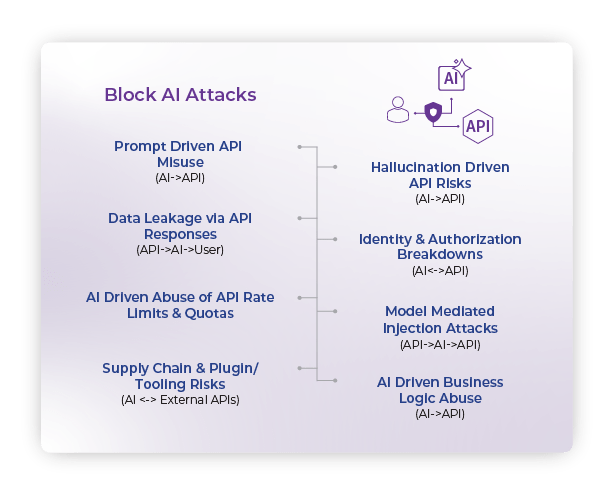
- Block AI to API threats
- Controlling AI agent interaction with APIs

Automation of API Security at the Speed of AI Coding Agents
Secure agent access, without losing control
Extend trust from API security to the AI execution layer

Secure agent access, without losing control
Extend trust from API security to the AI execution layer
Move fast with Agentic AI,
without sacrificing security, governance or trust
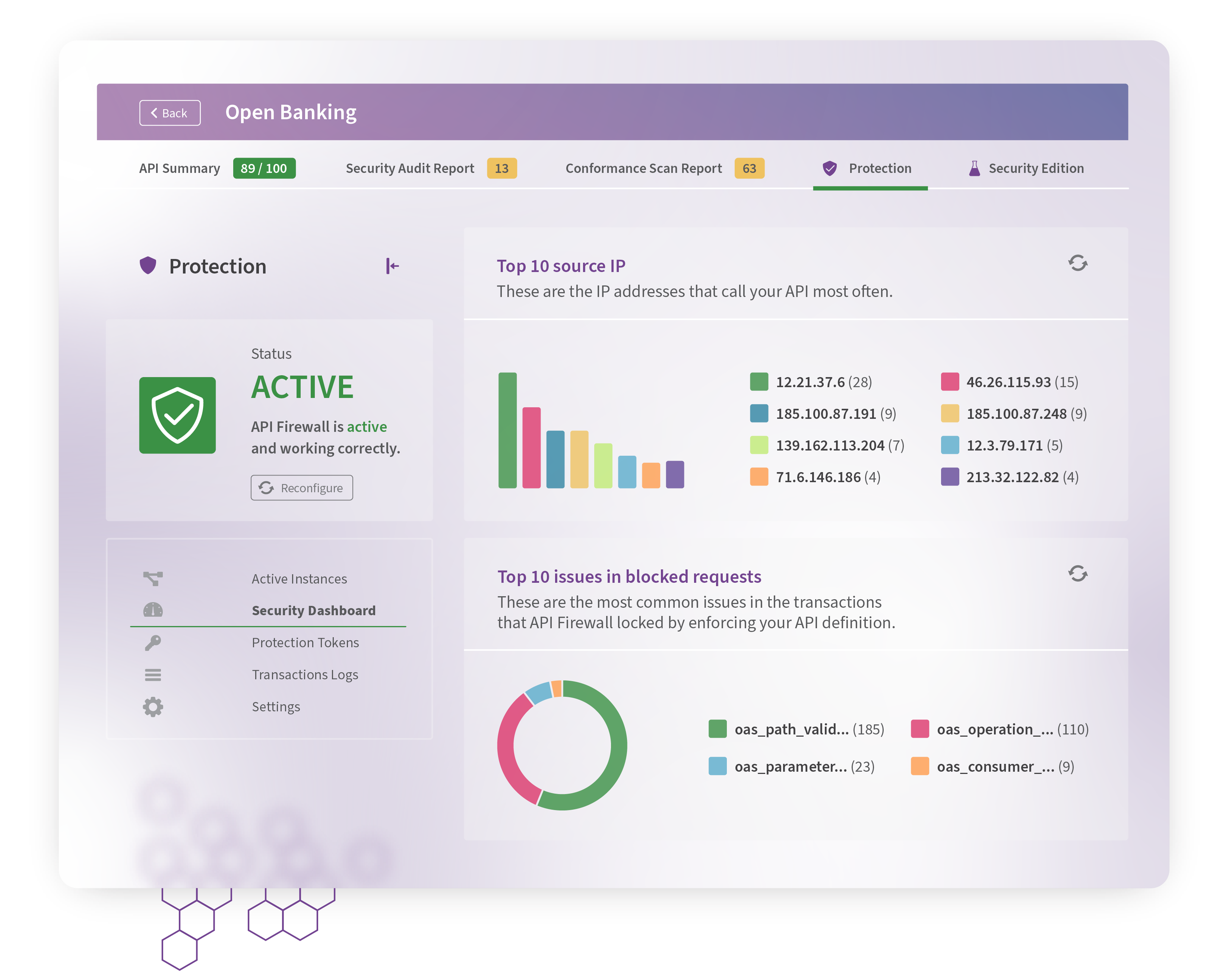
Immediately Block Attacks and Fix Vulnerable APIs
Stop ongoing attacks to vulnerable production APIs. Automate remediation and redeployment of all broken APIs to prevent further outages.
Whitepapers
Why API security-by-design is the correct approach to secure and protect your APIs
Building a Future-Proof API Inventory
How to create a Living API Inventory and avoid vendor lock-in. Learn More
42Crunch API Security vs Behavioral Analytics
Why using Machine Learning Alone Falls Short for API Security and Why
'Secure by Design' is Essential. Learn More
DAST vs API Contract Testing
What Security Teams Need to Know. Learn More
Industry Insights
Analyst Reports and eBooks covering API security
How 42Crunch solves API Security scaling requirements for Telecommunications
End-to-end API Security for the Software Defined Vehicle
The Ins and Outs of API Security and how to protect your APIs